AbstractFish discover water last.
Chinese Proverb
All firms use information technology (IT). Larger firms have IT organizations whose business function is to supply and manage IT infrastructure and applications to support the firm's business objectives. Regardless of whether the IT function has been outsourced or is resident within a firm, the objectives of the IT organization must be aligned to the strategic needs of the business.
It is often a challenge to balance the demand for IT against the available supply within the firm. Most IT organizations have little capacity to carry out activities that go beyond the incremental ones that are needed to run the immediate needs of the business. A process-ambidexterity framework for IT improves the IT organization's entrepreneurial ability, which in turn, better aligns the IT function with the business functions in the firm.
Process ambidexterity utilizes both process alignment and process adaptability. This article presents a framework for process alignment in IT. This is useful for understanding how the processes in Business Demand Management, a core component of the process-ambidexterity framework for IT, relate to those in IT Governance and IT Supply Chain Management. The framework is presented through three lenses (governance, business, and technology) along with real-world examples from major firms in the USA. Enabling process alignment in the IT function, and process ambidexterity overall, benefits those who govern IT, the executives who lead IT, as well as their peers in the business functions that depend on IT.
Introduction
This article presents a process-alignment framework based on the concepts of process ambidexterity. Then, it applies this framework to identify major processes and relationships that need to be aligned to enable an IT function to behave in an entrepreneurial manner.
Bot (2012) described a process-based perspective for balancing mainstream exploitation and new-stream exploration in the management of innovation-based technology firms. The resulting capability is known as process ambidexterity and it requires disciplined, agile, and lean business management. Process ambidexterity is a capability that utilizes both process alignment and process adaptability. Process alignment deals with intent, rigour, discipline, consistency, and maturity of the processes. Process adaptability deals with agility, responsiveness, flexibility, and customization of the processes (Bot, 2012). Bot and Renaud (2012a) subsequently examined how the concepts of process ambidexterity can be applied to the IT function within a firm whose mandate is to enable their firm’s business strategy and execution.
Most IT organizations are primarily focused on the supply chain of technology (IT Supply Chain) and often are unaware of the differences in need for technology across the firm’s business value chains (Business Demand). This article identifies the Business Demand Management component of the process-ambidexterity framework for entrepreneurial IT (Bot and Renaud, 2012a) as the pivot-point for enabling process alignment. Inward- and outward-facing process alignment is presented. This is followed by an introduction to the process-alignment framework for IT, along with a description of exploratory and exploitative process relationships through the lenses of governance, business, and technology.
Aligning Exploratory and Exploitative Processes in IT
In an IT context, mainstream exploitation refers to the evolution of the existing infrastructure and applications that service the current needs of the firm, while new-stream exploration refers to the entrepreneurial practice of new-technology adoption intended to enable new business activities or to transform the delivery of existing activities beyond the limitations of currently deployed IT solutions (Bot and Renaud, 2012a).
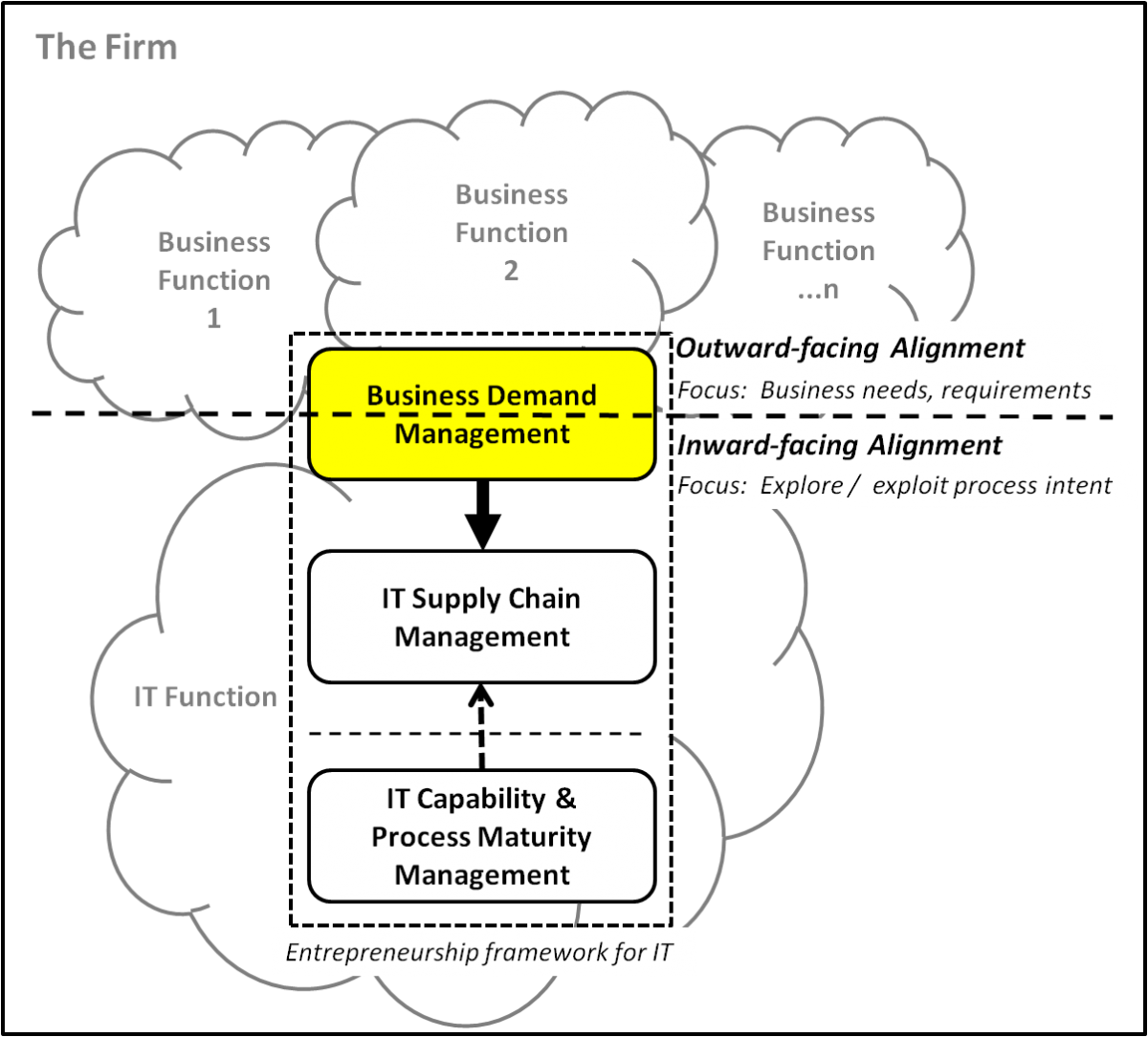
As shown in Figure 1, Business Demand Management is the pivot-point for process alignment in order to enable entrepreneurial IT. Business Demand Management must address both the outward-facing alignment of processes to the firm’s needs or business requirements (requiring rigour, discipline, and consistency) as well as the inward-facing process alignment between exploratory and exploitative process intent.
Figure 1. Inward- and outward-facing alignment in the context of the process-ambidexterity framework for entrepreneurial IT. Adapted from Bot and Renaud (2012a).
Outward-facing process alignment
From a practical perspective, aligning processes against business requirements involves identifying patterns in business requirements so that IT can be best employed to fulfill them. Ideally, a different IT solution would be used for each business pattern, however, this may be cost-prohibitive for many IT organizations. In practice, understanding business requirements is also difficult in large firms where no single person has a complete view of business requirements, let alone comprehends how they vary across several thousand applications. Many IT organizations struggle to obtain accurate business requirements because they fail to appreciate the difference between accuracy and precision.
It is often the case that an imprecise view of a business requirement is as accurate as a seemingly more precise version, yet an imprecise view is far easier to elicit from business users. For example, one business activity might require “high availability” for its applications while another might have a less stringent requirement. It is unlikely that their business users could express the requirement more accurately and any attempt to elicit greater specificity in terms of hours of downtime, frequency of failures, or other seemingly more precise quantification of that requirement are both unnecessary and irrelevant for the purposes of understanding how demand varies by business function. It is sufficient simply to categorize each requirement in broad terms because the purpose in gathering the requirement is to rapidly and accurately identify patterns in demand.
This phenomenon occurs whenever the perception of greater precision is illusory, for example, when business users simply cannot quantify their requirements past an undefinable limit. In practice, this is the natural state of affairs as most users have a hazy, yet definite view of their requirements. In such cases, a categorical instead of quantitative approach to elucidating requirements is best. Counting “trees” when trying to "see the forest" may be more precise but is unlikely to be more accurate.
Inward-facing process alignment
The objective of inward-facing process alignment is to align process intent, which ensures that exploratory and exploitative processes remain distinct with well-defined process interactions between them. Since the intentions of exploratory and exploitative processes are distinct, they should not be confounded by mixing both intents within the same process.
IT Process-Alignment Framework
Process ambidexterity requires an alignment framework that can be used to ensure disciplined IT process improvement. This is illustrated in Figure 2 and described in the following sections. Note that process ambidexterity utilizes both process alignment and process adaptability. This article covers the process-alignment aspect; a companion article (Renaud and Bot, 2012b) presents a process adaptability framework for IT.
Figure 2. Process-alignment framework for IT entrepreneurship
This framework has two dimensions:
- An entrepreneurship aspect, which delineates the domains of Business Demand Managment, IT Supply Chain Management, and IT Capability & Process Maturity Management.
- An orientation or focal aspect, which provides three foci (Governance, Business, and Technology) through which the processes in IT can be organized. Each of the three is useful for understanding process intent.
Business and Technology Focus
Exploratory practices support entrepreneurship when they are customer facing and value seeking. Entrepreneurship in IT requires processes for managing Business Demand by aligning to the firm’s priorities and for exploring new ways of satisfying that demand. Process ambidexterity results in a balanced application of both exploitative and exploratory processes for managing IT and enables the IT function to behave as an entrepreneurial entity regardless of whether the firm as a whole might be characterized as mainstream or entrepreneurial.
The IT function’s major challenge is to balance the demand for IT expressed by the firm with the supply of IT that the firm can afford. From an exploratory practices perspective, this means that the IT function should have exploratory processes for business-focused entrepreneurship as well as for technology-focused entrepreneurship.
The exploratory processes for business-focused entrepreneurship reside exclusively in Business Demand Management and the exploratory processes for technology-focused entrepreneurship reside exclusively in IT Supply Chain Management. In this context, “technology-focused” encompasses innovation involving both applications as well as IT infrastructure.
From an exploitative process perspective, the vast majority of exploitative processes in the IT function reside in IT Supply Chain Management. Because many of these exploitative processes are well-known and are part of established process frameworks such as ITIL, the authors will not discuss them further other than to note that they are mostly concerned with the operational management of IT infrastructure or the implementation of applications.
Governance Focus
There are also a few exploitative processes that reside in Business Demand Management and they are the processes that pertain to the governance and management of the IT function itself – as opposed to the management of IT infrastructure or applications. Bot and Renaud (2012a) previously determined that, since the purpose of IT Governance is to ensure that the IT function is aligned to the strategic objectives of the firm, the processes of Business Demand Management can significantly enhance IT Governance.
Lack of dynamic alignment to business objectives is the root cause of misalignment in which the IT function is so focused on operations that they do not realize that unmet needs are becoming more important than doing a better job of meeting existing needs. Business-focused processes are required to prevent lack of alignment and for ensuring that business needs are understood and prioritized, investment trade-offs are evaluated and weighed against existing initiatives, service-level objectives are established, and transition roadmaps are aligned to respond in time to support strategic business initiatives.
As the processes for Business Demand Management become formalized, the impact on IT Governance is profound because the processes in Business Demand Management assure dynamic and continuous alignment between the strategic priorities of the firm and IT decision making. Bot and Renaud (2012a) identified that, as long as the differing needs of each business function are incorporated into these processes, a dynamic approach to business alignment can be integrated into how IT is governed.
Since the IT priorities of a firm will vary greatly by business function, IT alignment can be measured and maximized by using a profile of Business Demand for IT by business function. Some business functions (such as accounting) may require very tight control and a low-risk computing environment characterized by high-availability computing clusters, while others (such as sales) may require more flexibility in using new technologies for messaging, collaboration, and mobility. IT Governance that allows for variation by business function can transcend these differences while maintaining a common governance framework and ensuring that the consumption of IT resources is aligned to investment priorities for each business function.
Interactions exist between the exploratory and exploitative processes. The relationships between the exploratory and exploitative processes, and their fit within the IT process-alignment framework, are summarized in Table 1. The following sections describe the interactions in further detail, as seen through the governance, business, and technology foci.
Table 1. Relationships between exploratory and exploitative processes
|
Focus |
Exploratory Process |
Aspect |
Related Exploitative Processes |
|
Governance |
Demand Profiling |
Business Demand Management |
Capacity Management |
|
Resource Balance Analysis |
Business Demand Management |
IT Chargeback |
|
|
Business |
Application Portfolio Alignment |
Business Demand Management |
Application Portfolio Rationalization |
|
Business Solution Management |
Business Demand Management |
IT Service-Level Management |
|
|
Technology |
IT Solution Management |
IT Supply Chain Management |
IT Product Management, TCO Analysis |
|
New Technology Assessment |
IT Supply Chain Management |
New Product Introduction, IT Standards Management |
Process Alignment as Seen Through the Governance Lens
This section uses the governance lens to identify both the exploratory and exploitative processes that reside in Business Demand Management.
Demand Profiling and IT Capacity Management
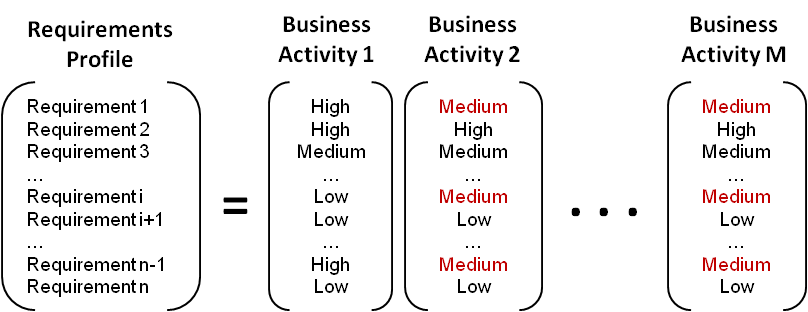
Demand Profiling is an exploratory process for managing IT requirements by business activity using a common profiling method across all business activities. Demand Profiling allows for patterns of differences and similarities between business activities to be revealed. This process is illustrated conceptually in Figure 3, which shows that Business Activity M has the same demand pattern as Business Activity 2.
Figure 3. Conceptual demand profile of business activities
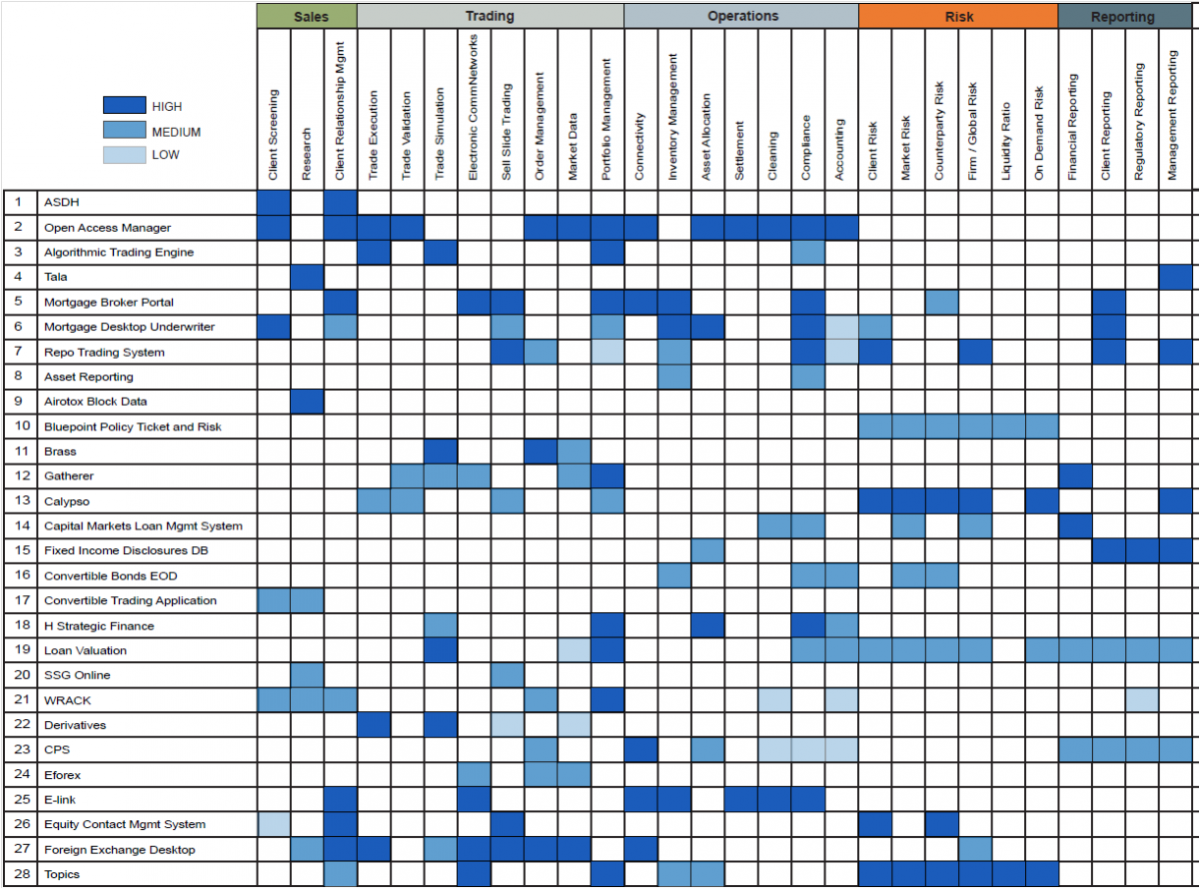
In practice, a range of 20–50 business requirements is sufficient to characterize demand. For example, a demand profile for over 160 business activities was created for a firm-wide set of 50 IT requirements at a major investment bank. This demand profile, as subset of which is shown in Figure 4, was used to group patterns in demand that were subsequently matched to the capabilities of different types of IT data centres. This identified the optimal placement of business-activity-related processing to the data centres that best satisfied their needs. Demand Profiling also revealed that processing for lower-priority business activities could be relocated to lower-cost regional data centres without impacting business needs.
Figure 4. Example: Subset of a demand profile in investment banking (Excerpted from The Lanigan Group’s Demand Profile for Investment Banking. All rights reserved. Used with permission.)
Demand Profiling is related to, but distinct from, the exploitative process of IT Capacity Management. The purpose of IT Capacity Management as defined in ITIL is to monitor and trend the change in growth in consumption of different IT resources so that sufficient capacity for future increases in consumption of these resources can be planned in advance.
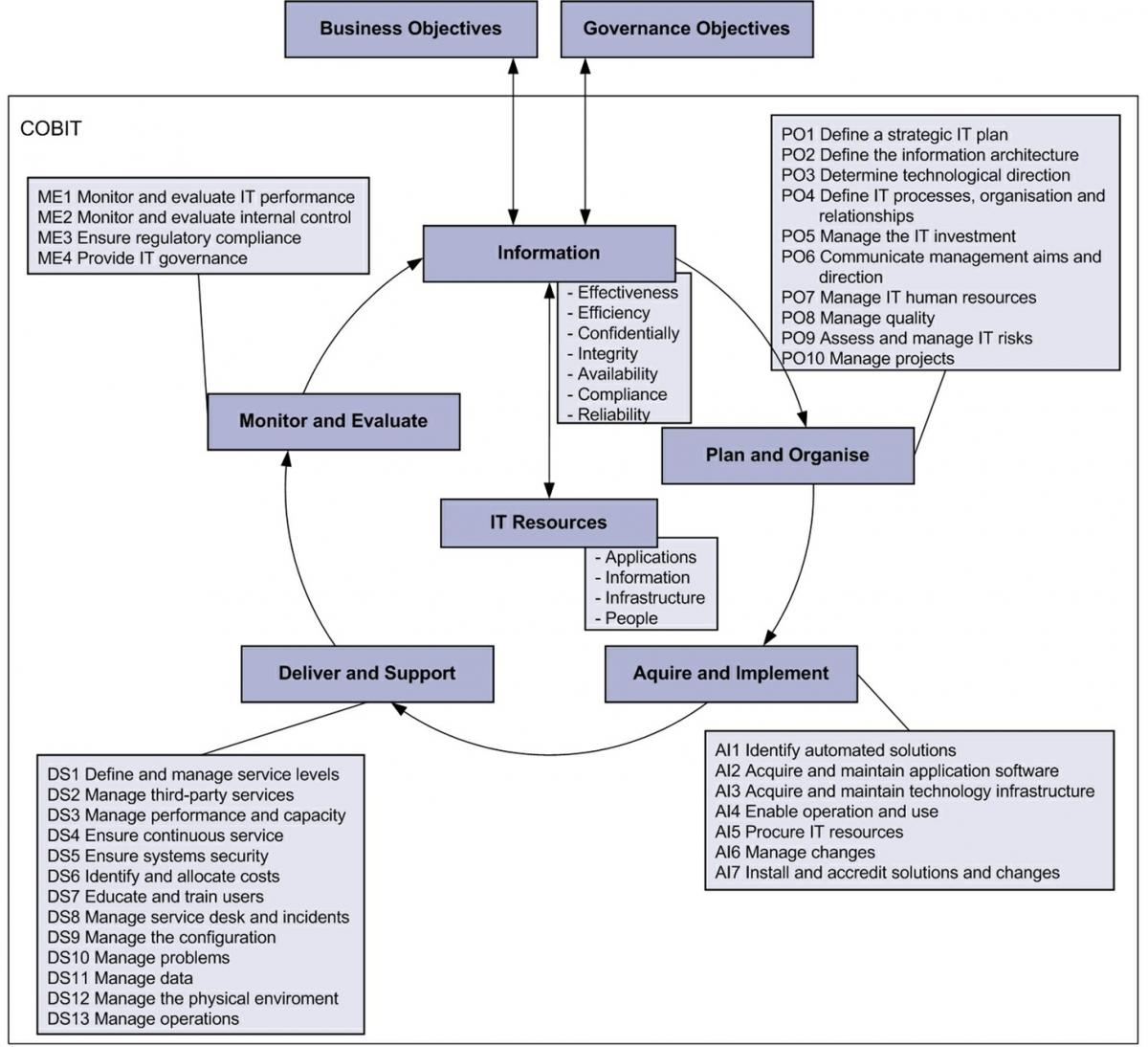
The focus of IT Capacity Management is to avoid resource exhaustion in the IT Supply Chain, whereas Demand Profiling is focused on understanding patterns in demand that ultimately lead to the consumption of those resources. IT Capacity Management is also related to the various IT management, planning and budgeting processes defined by the COntrol OBjectives for IT (COBIT) framework (See wikipedia.org/wiki/Cobit and isaca.org/COBIT/Pages/.)
COBIT defines a process framework based on a firm’s internal control system for the IT function. Within this framework, a set of 34 high-level control objectives are defined, each with a corresponding process, and grouped into four domains: planning and organization, acquisition and implementation, delivery and support, and control monitoring, as illustrated in Figure 5.
Figure 5. COBIT defined processes (Executive Summary for COBIT 4.1 (2007). ©ITGI. All rights reserved. Used with permission.)
The processes in the COBIT Monitoring domain are exploitative governance processes that reside in Business Demand Management, as are most of the processes in the Planning and Organization domain (the exceptions being PO3, PO7, and PO10 that belong in the IT Supply Chain Management and Process and Capability Management parts of the framework shown in Figure 2). The remaining COBIT processes are exploitative processes that reside in IT Supply Chain Management.
COBIT does not define any exploratory processes and since COBIT is well-defined, we will not discuss these processes further.
Resource Balance Analysis and IT Chargeback
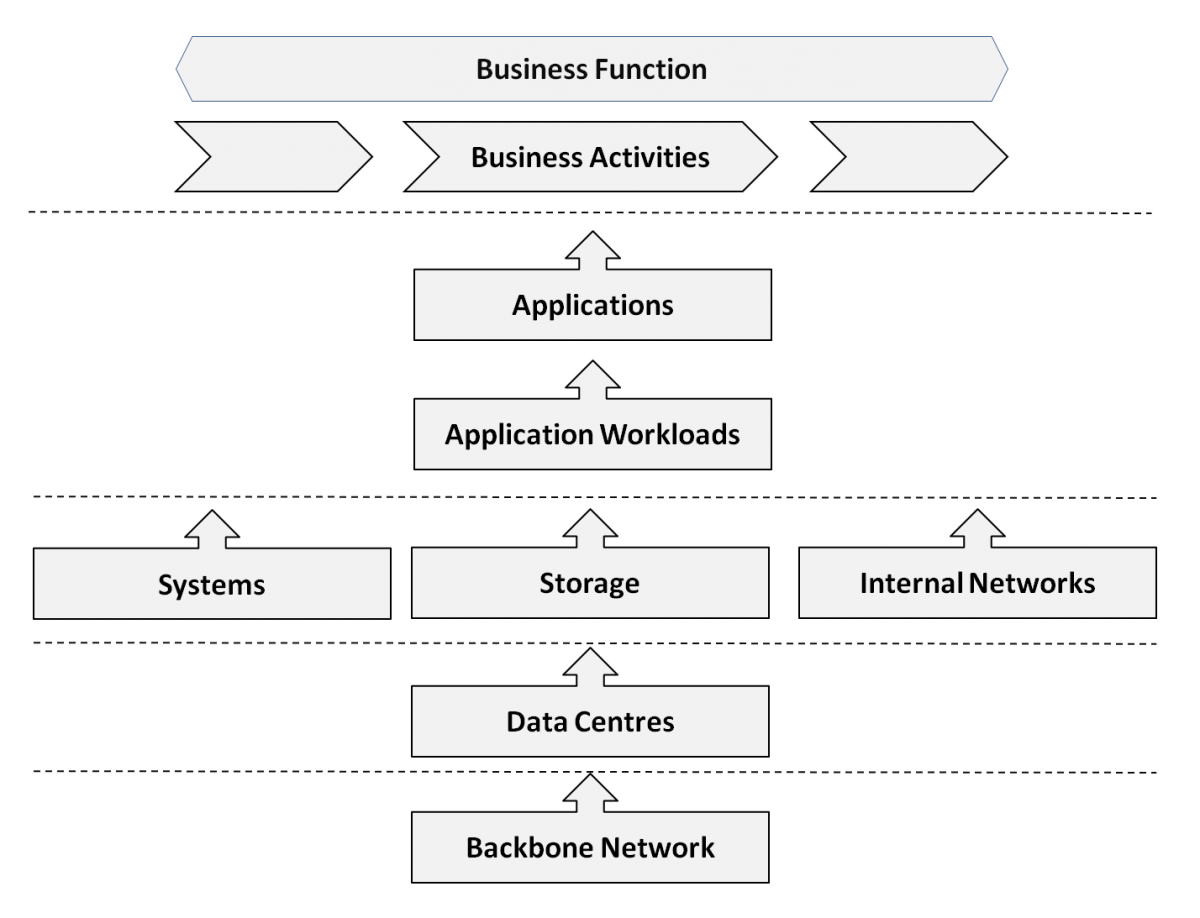
Resource Balance Analysis is an exploratory process that ensures that the allocation of IT resources is commensurate with business priorities. This process examines how the inventory of IT resources rolls up by the business function that it supports and then examines the proportional allocation of resources by business function in relation to business investment priorities for each business function. A typical rollup hierarchy is illustrated in Figure 6.
Figure 6. Rollup levels for Resource Balance Analysis
For example, an investment bank might view both its Accounting and Trading business functions as strategic, but it might be more interested in investing in IT to enable the Trading function to drive more revenue while controlling the cost of IT to support the Accounting function. Being able to roll-up a view of the extent of the IT Supply Chain devoted to serving each business activity within Trading and Accounting can provide valuable insights into where resource allocation may be viewed as out-of-proportion compared to the firm’s business priorities.
The related IT Governance process is IT Chargeback, which is an exploitative process that accounts for consumption of IT resources so that cost allocations can be charged back to the business functions that employ them (Drury, 1997). Even though Resource Consumption Analysis may be able to use the data produced by an IT Chargeback process, it is a distinct process because it explores the extent to which chargebacks reflect desired levels of business investment in IT by business function. This can lead to identifying that IT solutions for a particular business activity are too costly for the benefit obtained, leading to potential outsourcing of the solution via a cloud or hosting provider.
For example, Resource Balance Analysis performed by the first author (Renaud) at a Fortune 500 company found that a significant percentage of application servers in expensive data centres were occupied by low-priority business activities that could be more cost-effectively hosted in lower-cost, remote facilities – such as an internal private cloud.
Note that Resource Balance Analysis should not be confused with the forensic process of Resource Consumption Monitoring which is an exploitative IT Supply Chain Management process that ensures that IT resources are operating within their expected operational parameters.
Process Alignment as Seen Through the Business Lens
This section identifies the business-focused exploratory processes that reside in Business Demand Management, and links them to corresponding exploitative processes that are found in IT Supply Chain Management.
Application Portfolio Alignment and Rationalization
McKeen and Smith (2010) describe the benefits of treating IT applications as a proactively managed portfolio. This is common practice within the IT function in the financial services industry and in other firms where IT is seen as an investment into the business of the firm.
Ignaganti and Behara (2007) describe a practical method for aligning the application portfolio in a service-oriented enterprise architecture by relating application functionality to the business value chain and using a services layer to refactor applications. The first author of this article (Renaud) observed that applying this method at Wachovia resulted in a 50% reduction in application development and sustaining costs as well as faster time-to-market for new business products. Applying the business lens in the process-alignment framework, we can identify two distinct processes involved in their method.
Application Portfolio Alignment is an exploratory process that maps each application to the business activities that it serves and then examines the opportunity for rationalizing applications that service the same business activities. Within any firm, small applications may service a single business activity, while larger applications may service multiple business activities. Even larger application suites such as SAP or Peoplesoft may service entire business functions. The relationship between applications and business activities is illustrated in Figure 7. In a large firm with hundreds or thousands of applications, many of these applications will overlap in functionality. The root cause of application overlap is usually due to parallel implementation of similar applications to support different business products.
Figure 7. Example of Application Portfolio Alignment in financial services using Adaptivity (Adaptivity, Inc.’s Design Studio™ [Planning Studio™] application portfolio analysis software product. Adapted and used with permission.)
For example, Application Portfolio Alignment conducted by the first author (Renaud) at Sprint found that over two dozen different applications existed for the same business activity of billing. Each billing application had been developed independently as an expedient means of introducing a new telecommunications network service offering (managed routers, frame relay, Internet access, business voice, consumer voice, etc.). A similar exercise at Wachovia found over a dozen similar loan management applications, each one supporting a different type of loan (mortgages, business loans, investment financing loans, etc.).
In general, multiple overlapping applications occur whenever a unique application is developed or purchased to service the needs of a business product and more than one such business product exists for the same business activity.
Since most firms have established configuration management databases (CMDB) that track the allocation of resources by application, it should be observed that the process of Resource Balance Analysis is straightforward once Application Portfolio Alignment has identified the conjoint relationships between applications and business functions. This enables a two-step mapping involving a rollup of resources to applications and then a rollup from applications to business activities or business functions (allocating resources appropriately when multiple business activities are serviced by an application).
Application Portfolio Rationalization is the follow-on exploitative process that reduces application overlap by either decommissioning applications, refactoring them, or truncating their functionality to eliminate overlaps. Application Portfolio Rationalization is typically a multi-year process whereas application portfolio analysis is a process that can complete in under a year in a firm that has several thousand applications.
Business Solution and Service Level Management
Business Solution Management is an exploratory IT-engagement process that assists business functions in choosing the right set of IT products that best meet their needs. The engagement process facilitates adoption of existing IT products by internal users and identifies gaps in the IT product portfolio. Business Solution Management is exploratory because it is focused on exploring the needs of the business to determine if existing IT products can be used to create the solution that the business needs or whether new products are required. Business Solution Management also identifies the most appropriate service and recovery levels for new business needs.
Business Solution Management should not be confused with the exploitative, IT Service Level Management process, which is an ITIL-defined process ultimately based on delivering desired service levels against a pre-defined catalog of IT products and services that can be ordered from the IT function (Mazvimavi and Benyon, 2009). IT Service Level Management is appropriate when a business function requires more of the same kind of IT product that it is already using (for example, provisioning a new database and server), while Business Solution Management is more appropriate when new or changed business needs (other than scale) must be met.
Process Alignment as Seen Through the Technology Lens
Solution and Product Management
IT Solution Management and Product Management in IT is the definition and delivery of IT product solutions to the internal customers within the firm. IT Solution Management is the exploratory process for managing how IT product technologies get integrated into solutions to meet business needs, whereas IT Product Management is the exploitative process for managing the lifecycle of how IT product technologies are selected, standardized, and transitioned across new versions over time (Espinosa et al., 2009).
Just as product companies cannot satisfy all needs in all potential markets, the IT function cannot support the bespoke needs of all internal users and must determine the optimal balance between introducing products and meeting priority needs. Similar to the process of product management in technology product companies, successful IT Solution Management and Product Management requires:
- Clear delineation of the addressable market for each product. In an IT context, this involves determining which business activities would use each product and whether there is sufficient product appeal to enough business activities to justify the time and expense of product creation and support.
- Identifiable value proposition for each product. In an IT context, this involves identifying the business requirements that each product satisfies best.
- Attention to total product cost. In an IT context, the total cost of ownership of a product must include facilities, power, cooling, support labour, and other attracted costs. For example, a total cost of ownership (TCO) analysis conducted by the first author (Renaud) in a major US financial institution found that data centre-related costs were two-thirds the total cost of an IT storage solution. This insight led the IT function to configure higher-capacity disks in its storage area networks (SANs) and abandon the prior engineering practice of using more, smaller disks to reduce I/O latency. The larger disks meant that less rack space would be consumed by the petabytes stored in its SANs, significantly reducing TCO while only slightly increasing latency due to the faster rotational speeds on the larger drives.
Business changes require ongoing changes to IT solutions, which can be implemented in most IT organizations by establishing solution and product management processes. In firms where IT Product Management already exists, the product management process invariably must become more customer facing and less IT-infrastructure facing. This is difficult because IT Product Management is inherently an exploitative process that is concerned primarily with managing the evolution of existing product technologies. Meanwhile, IT Solution Management is inherently an exploratory process that determines whether product variations can be integrated into a generic IT solution. Best practice in process alignment indicates that a separate, exploratory process is required for IT Solution Management and that it is better to design appropriate process interactions between solution and product management than to try to combine an exploratory process with an exploitative process.
To assure this outcome, key metrics in any balanced scorecard should include at least one leading indicator that measures alignment to business objectives/requirements and at least one lagging indicator that measures the incremental benefit from better delivering to aligned priorities.
Technology Assessment
The introduction of new technologies into the firm is typically managed by the CTO organization with the IT function. It is important to recognize that there are three distinct aspects to new technology introduction:
- New Technology Assessment is the exploratory process of managing how new technologies can be employed to better meet business needs. This process must consider potential opportunities for cost or productivity benefits for using new technologies to meet existing needs, or to better service unmet or poorly met needs.
- IT Standards Management is an exploitative process of managing the selection of normative standards and supported product suppliers for the firm’s IT. For example, Oracle or MySQL might be selected as the “standard” relational database technology to be used firm-wide. Most firms will define tiers of standards based on their lifecycle of adoption such as: emerging/experimental (requiring special approval), standard (no approval required), supported (may be used but no new purchases allowed), sunset (used within the firm but unsupported by IT).
- New Product Introduction is the exploitative process of managing the controlled introduction of new technologies into the IT Supply Chain. New Product Introduction is well established as a process in manufacturing and telecom operations and is also sometimes referred to as "release management" in IT. This process starts with a technology that has already been selected for introduction (as a result of either a New Technology Assessment process or user-led technology selection), and it evaluates potential sources of supply, selects vendors, engineers appropriate configurations, conducts field trials, negotiates support and maintenance agreements, trains operations staff, and generally eases the impact of introducing a new technology into the operational IT environment.
Conclusion
This article provides a process-based framework for enabling process alignment in IT. This article makes three contributions:
- It identifies the Business Demand Management component of the process-ambidexterity framework for IT entrepreneurship as the focal component that enables process alignment.
- It presents a practical and real-world framework for process alignment in IT.
- It identifies the exploratory and exploitative process relationships though the lenses of governance, business, and technology.
Process alignment and process adaptability are the key components of process ambidexterity. A companion article (Renaud and Bot, 2012b) presents a process adaptability framework for IT. Together, these pave the way for growing the capability of process ambidexterity, which in turn improves the performance of the IT and business functions, and the firm overall.
Acknowledgements
This article uses the terminology of “business value chains”, “business functions”, and “business activities” established by Porter (1985).
Demand Profiling is based on a prior unpublished collaboration with Sheppard Narkier at Wachovia and is based on his earlier work at UBS Investment Bank.
Keywords: exploitation, exploration, IT function, process alignment, process ambidexterity